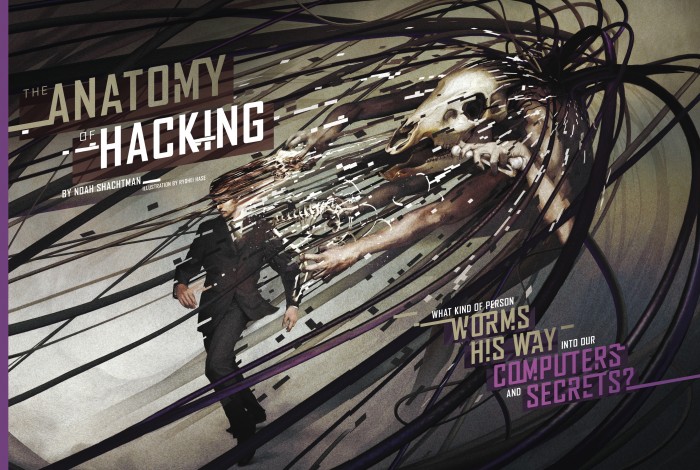
The Anatomy Of Hacking
November, 2011
HEN JAKE DAVIS APPEARED IN A London court in August, it seemed as though Scotland Yard had dragged the 18-year-old hacker straight from central casting. It wasn't just Davis's pale, skinny appearance. Nor was it his continued residence in his mother's home or his smartest-kid-in-the-room arrogance. It was that Davis's crime was a classic nerd's revenge: a fake article on The Sun's website announcing the death of Rupert Murdoch. Davis fits our stereotype of a hacker, but these days he's hardly typical. It no longertakes an Asperger-y genius to break into an online bank; in fact, it's not much harder than setting up a website. And the guy trying to get into the mainframes of the Defense Department might have more in common with James Bond than with Mark Zuckerberg. Look out at the cybersecurity landscape and you'll find fourtypes of people compromising computers. Each has his own motivation, skill set and means of attack. And only a few still live with Mom.
TCRDDKS
These are the nasty
men making custom software to capture your banking password. In particular, they use "botnets" (chains of
millions of enslaved computers) to spew out spam and authentic-looking online storefronts ("phishing" sites) to trick you out of your money. But these online criminals aren't exactly masterminds.
The Zeus and SpyEye crimeware kits make it easy to build a program that can scrape a computer for sensitive data. With a few mouse clicks, a wannabe thief can configure what he wants his malicious code to do—i.e., which banking sites he wants to monitor, what information he wants to grab and how he wants that information sent back to him. And if the thief gets stuck, the crimeware firms are well-known for providing quick answers to all sorts of technical questions. No wonder the security group Sophos finds 150,000 new malicious software variants a day.
There's also a huge array of companies that will help the crook pull off his cybercapers. For instance, if he wants to sneak crimeware onto your computer, he can hire a company to hide it in what seems to be an ordinary online ad, which then gets placed onto a legitimate website through a series of front companies. (The low, low rate: $7 for 1,000 infections.) Or the thief can rent out space on a botnet—that runs $9 an hour—which uses its compromised computers to send out spam. Maybe the messages tell recipients to update their PayPal or Linkedin accounts; maybe they lure them with the promise of cheap drugs or enhanced man parts. Either way, click on that link and you're screwed: The crook now has control of your machine.
Think it can't happen to you? Guess again. While statistics on online crime are unreliable, the British government
estimates that online thieves, scammers and industrial spies cost U.K. blokes and businesses $43.5 billion in the past year alone. For average consumers—and really for the internet as a whole—the rising tide of cybercrime is the most serious online threat. You'll hear old-timers such as Defense Secretary Leon Panetta wring their hands about a digital Pearl Harbor—some kind of digital doomsday. And there is some reason to worry. (More on that later.) But for you and me, the immediate concern is that the internet could turn into a cyber South Bronx circa 1979—a neighborhood where crime is so commonplace that we stop going there.
In the security community, the rap is that these crooks are mostly foreign—living behind the old Iron Curtain or somewhere in Shandong province. Last year the FBI worked with authorities in Kiev to nab five Ukrainians who had used Zeus to steal nearly $70 million. But even if the criminals are based abroad, they often rely on American infrastructure. Take hosting companies, which provide the servers that make digital information available to the rest of us. According to the research firm HostExploit, 23 of the 50 most criminally connected companies—the ones hosting the sham pharmacies and spam generators—are American. When the Silicon Valley-based McColo hosting company was taken down, worldwide spam dropped 65 percent overnight.
It would also be naive to think that cybercrooks don't operate in the United States. The brains behind the biggest online credit-card-fraud scheme, a 39-year-old former security consultant named Max Butler, was nabbed in the high-end corporate apartment he shared with his girlfriend in San Francisco. He was recently sentenced to 13 years in the federal pokey, one of the longest sentences of its kind. But considering he helped rack up $86 million in fraudulent charges and single-handedly took over the market for online financial scams, some people think he got off easy.
SABOTAGE: SABOTS
egend has it the word sabotage derives from sabot-wooden shoes that disgruntled French workers supposedly dropped into their employers' machinery. Bristling at the work discipline imposed on them by their bosses, these workers chose not to rebel actively but preferred to screw things up through the "collective withdrawal of efficiency." By destroying
profits, sabotage became an insidious way for labor to assert some form of control over the means of production. The practice endures in the workplace today. As the old Wobbly slogan had it, "Good pay or bum work." Subsequent saboteurs-including those eco-warriors inspired by Edward Abbey's legendary Monkey Wrench Gang-all owe a debt to these wooden shoes.
'SPIES
They use some of the crooks'
tricks—the e-mail come-ons, the fake websites and the tricky programs that grab private information. But these aren't common criminals. The e-mail appears to be sent by the guy in the next cubicle (and reads like something he wrote),
and the link you're supposed to click looks like the presentation you're making at your next big meeting. All the while, the data that are being slurped up are your company's most vital secrets. No company is safe. In the past few years, Lockheed, Morgan Stanley and General Electric have all been victims of industrial espionage. Because of the spies' sophistication, foreign governments—specifically the one in Beijing—are suspected of backing these online espionage rings. The idea isn't just to drain billions of dollars from the U.S.; it's a method of upgrading an industrial economy into
an information one, using our know-how. Rhode Island Democratic senator Sheldon Whitehouse, who chaired a classified task force on the subject, called it "the biggest transfer of wealth through theft and piracy in the history of mankind."
Not that Whitehouse can prove anything. Even if you can strip away the anonymous e-mail addresses, proxy servers and encrypted messages, it's still impossible to tell who's sitting at a particular keyboard (let alone who's funding that person). Muddying things further is the fact that spies can hide themselves in the noise of criminal behavior or simply outsource an operation to crooks.
Still, there is circumstantial evidence to follow. In 2009, for instance, someone slipped into the extranets of leading American energy companies, stole executives' credentials and used those passwords to exfiltrate billions of dollars' worth of information on oil deposits. The tools used to pull off the
so-called Night Dragon break-ins were advertised on Chinese websites. The person who provided the hosting services was based in Shandong province (though the servers themselves were on U.S. soil). The people scouring the energy company networks "operated on a strict weekdays, nine-to-five Beijing time-zone schedule," according to a researcher at the McAfee security firm. And so you don't need to be an ace spy hunter to draw some conclusions about Night Dragon's origins. The spies aren't limiting themselves to industrial capers, either. The deputy defense secretary recently announced that 24,000 sensitive Pentagon files were snatched by "foreign intruders," and the Office of the Secretary of Defense's unclassified e-mail system has been compromised repeatedly. But the U.S. government isn't just a victim. Washington maintains a 36,000-person intelligence organization that's all about compromising computers and snooping on conversations. It's the mega-secret National Security Agency. And it (allegedly) has the ability to capture 1.7 billion separate communications a day. The NSA is supposed to stay focused on monitoring our enemies. But it doesn't always work like that. Since 9/11, everyone from average joes to an undisclosed congressman have been caught in the drift net.
SABOTAGE:
he Luddites used mallets to bust up textile frames. In March 1B11 a group of workers broke into shops in Nottinghamshire to smash labor-saving machines used to make stockings. Claiming loyalty to the mythical Ned Ludd, these artisans
challenged relations between labor and capital. Luddism spread throughout much of industrial England. Historian E.J. Hobsbawm called it "collective bargaining by riot." Lord Byron said sarcastically, "Men are mare easily made than machinery."
'SOLDIERS
Until recently,
it was the spies who had the Pentagon most worried. Not only is the American military the most network-dependent on the planet, with everything from drone video to battle plans relayed digitally, but Pentagon cybersecurity, in a word, sucks. A lowly private is charged with giving hundreds of thousands of classified files to WikiLeaks. A rudimentary worm called agent.btz is still winding its way through the Defense Department's networks, three years after it was first found. And central management of the Pentagon network—a common feature in most big companies—is still a dream.
At the moment, however, there's a new bogeyman, perhaps of our own creation. Last year, inspectors at the International Atomic Energy Agency discovered that the centrifuges at the uranium-enrichment plant outside of Natanz, Iran were failing at more than 10 times the normal rate. Turns out, those failures were deliberately triggered by a worm known as Stuxnet. It was able to hijack an industrial control system and issue orders to spin any attached centrifuges out of sync until they broke. In other words, Stuxnet was an honest-to-God cyberweapon—code that caused real-world damage. Depending on whom you believe, the arms makers were Israeli, American or both. But what's definitely true is that the same kind of industrial control systems used in Iran are also used here in the United States. They control everything from the power grid to the water supply.
Translation: We're vulnerable too. That's why Leon Panetta and others are so spooked.
For now, it's mostly a theoretical concern. The countries that have the ability to pull off a Stuxnet II have a lot at stake in U.S. stability. And a worm can go rogue; Stuxnet infected hundreds of thousands of computers that have nothing to do with Tehran's nukes. But it isn't hard to imagine the situation changing.
Consequently, Pentagon officials have announced that an online attack against our grid could be treated like a
physical attack—i.e., if you send us a logic bomb, we will send you a satellite-guided, high-explosive one. Implementing the plan would be a nightmare, of course. It makes the major assumption that you can identify the perpetrator of the online attack. Plus, if Stuxnet was an American operation, doesn't that open us up to Iranian retaliation? If we're not careful, it might not be American code that goes Frankenstein on us. It might be American policy as well.
SABOTAGE: ANARCHIST BOMBS
he year 1919 saw a series of bombings in the U.S. as anticapitalist sentiment reached its apex. Organized anarchists-primarily a group af Italian immigrants known as Galleanists-went on to plant bombs in various corridors of power. For a while,
revolution seemed possible in the U.S. The inevitable police response was strong-the so-called Palmer Raids set the standard for future witch hunts-butthe image of the mustachioed bomb-throwing anarchist endures in our culture as a symbol of mayhem.
JOKERS
Back in the day,
T ¦ ¦ ¦ W mm Um9 "^. hackers didn't break H ¦ I I I |V | |% «^ mt0 networks for cash E U LJ IlLJl U or country. They did it
for fun—and maybe as a fuck-you to the grown-ups of the world. That spirit has been rekindled, in a way, by two collectives that
have grabbed headlines with their high-profile hacks: Anonymous and LulzSec. Anonymous started out as a prankster cabal, pulling tricks such as uploading flashing pictures to an online epilepsy forum. Next, Anonymous started screwing with the Church of Scientology, crashing its websites and protesting in Guy Fawkes masks outside its real-world centers. Then came Operation Titstorm, a protest against the Australian government's online pornography laws. Things got more political from there. In December 2010 Anonymous took down the
websites of Visa, MasterCard and PayPal because the companies stopped processing WikiLeaks donations. In February the hackers broke into the network of security contractor HBCary and published the firm's nutty proposal to discredit WikiLeaks' supporters. Oh, and they published tens of thousands of the firm's e-mails, both received and sent. Fuck you, Grandpa.
LulzSec (lulz means "laughs" in netspeak) got together in May; Jake Davis, using the handle Topiary, quickly emerged as its shit-talking spokesperson. It went after Fox News, freed sensitive files of the Arizona state police and briefly knocked CIA.gov offline. A few weeks later, LulzSec announced its breakup. But when the News of the World phone-hacking scandals went nuclear, it couldn't help but hack the website of another Murdoch tabloid.
As you'd expect with far-flung, loosely affiliated political-prankster movements, the sophistication of these attacks varies wildly. Many rely on the bluntest of instruments—the "distributed denial of service" attack, which overloads a website with junk traffic. Anonymous's tool for marshaling that traffic was particularly lame, exposing the IP addresses of those who participated.
The HBCary hack, on the other hand, was slick. So was the breach of Sony Online Entertainment, which may have
disclosed 24.6 million users' personal information. Anonymous swears it wasn't behind this intrusion. However, that hasn't stopped international authorities from launching a worldwide witch hunt for Anonymous and LulzSec. Arrests have been made in the Netherlands, Spain, Italy and Switzerland.
In July, U.S. officials nabbed 14 alleged Anonymous supporters in California, including a 42-year-old woman and a 36-year-old man. (As if you needed more proof that the hacker stereotype is obsolete.) That same day, Scotland Yard arrested a suspected LulzSec member in South London. Tflow, as he's known online, is 16 years old. Authorities haven't publicly released the young man's name or whether he was captured in his mother's basement.
SABOTAGE:
n the early 1970s John Draper discovered
that toy whistles found inside boxes of
Cap'n Crunch cereal generated a tone of
2600 hertz, enabling him to access Ma Bell's
long-distance lines forfree. Draper claimed he
was interested only in exploring the telecom system, but he was subsequently arrested and convicted on wire fraud charges. For its spirit of mischief and curiosity, hacker culture owes a great debtto Draper.
THE RIGHT STUX
Last yearthe covert computer worm Stuxnet, a weapon of mass disruption, infected the computer systems at Iranian nuclear facilities in Natanzand Bushehrjat right).
MASKED CRUSADERS
Three members
of Anonymous
(near right) and
LulzSec shit stirrer
Jake Davis.